Gembet Privacy Policy: What Happens to Your KYC Documents
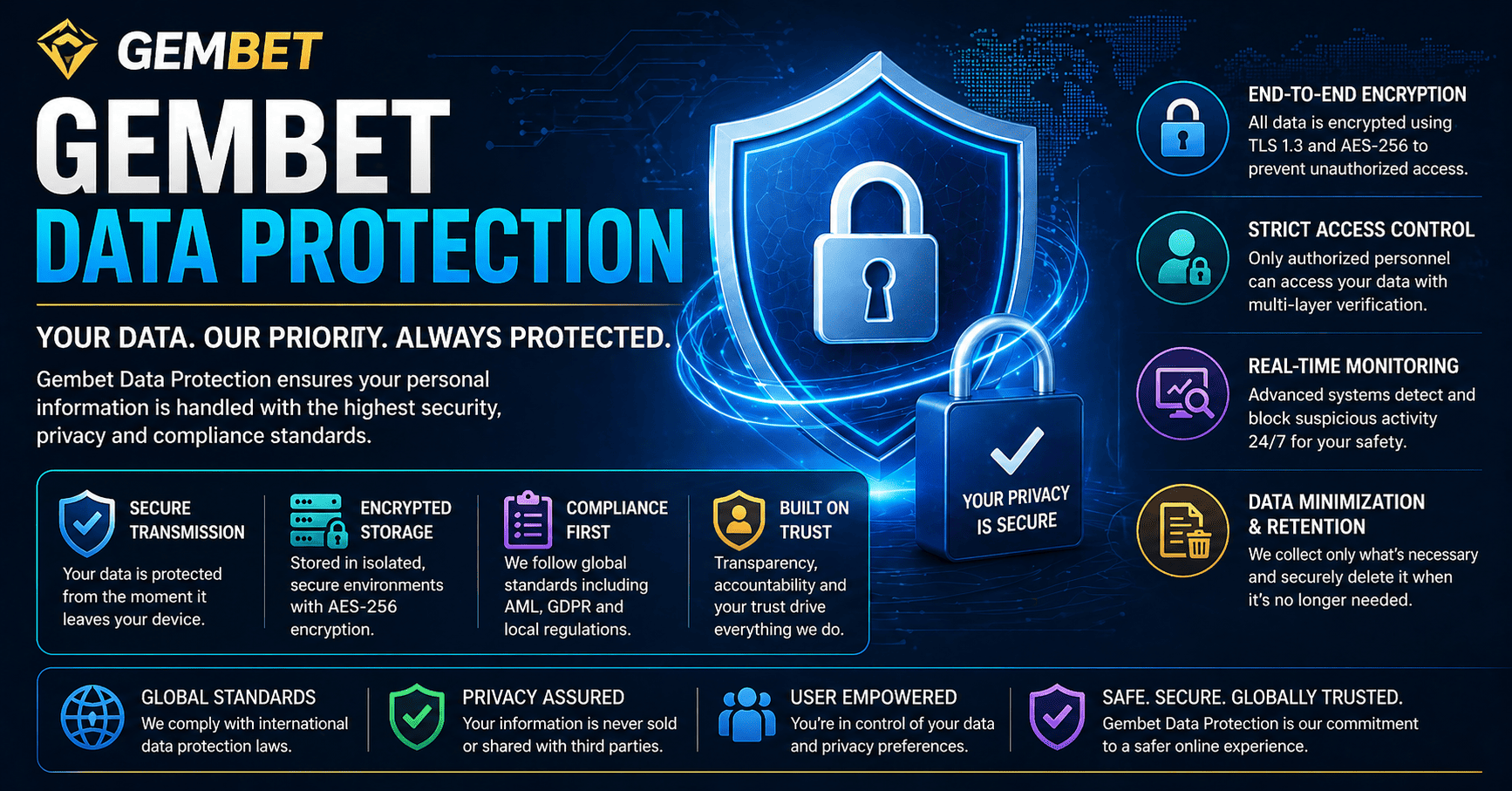
Gembet Data Protection ensures that all personal information, documents, and transactions are secured through advanced encryption, controlled access, and continuous monitoring systems.
Gembet privacy policy mandates provide the framework for how your sensitive information is managed from the moment you click upload. While the Know Your Customer (KYC) process is often viewed as a simple hurdle before a withdrawal, it represents a complex interaction between regulatory compliance and digital security. Understanding how your documents are handled is essential for maintaining safety in 2026.
The verification process serves a dual purpose. It protects the platform from fraudulent activity and ensures that data protection standards meet international requirements.
- Identity verification prevents underage access and identity theft.
- Compliance with AML regulations requires verified user profiles.
- Security protocols ensure documents are not exposed to unauthorized personnel.
- Data minimization limits the amount of information requested.
The Initial Upload and Encryption Phase
The gembet privacy policy is activated the moment a document is uploaded. Files are transmitted through encrypted TLS 1.3 connections, ensuring data is secured before leaving your device.
Once received, files are protected using AES-256 encryption at rest. Even if storage systems are accessed, the data remains unreadable without proper decryption keys.
- TLS 1.3 encryption secures documents during transfer.
- AES-256 encryption protects stored files.
- Checksum verification ensures file integrity.
- Isolated storage separates KYC data from gaming systems.
Who Has Access to Your Documents
Access under the gembet privacy policy is limited to specialized compliance teams. General support staff cannot view sensitive documents.
Automated systems assist with verification, reducing direct human exposure to personal data.
- Role-based access control restricts visibility.
- Audit logs track every document interaction.
- Two-factor authentication secures staff access.
- Automated tools reduce manual handling of data.
What the Platform Does Not Do With Your Data
The gembet privacy policy clearly states that personal data is not sold or used for unrelated purposes.
- No selling of data to advertisers.
- No use of documents for marketing.
- No sharing with unauthorized third parties.
- No unnecessary long-term storage of files.
Data Retention and Deletion
The gembet privacy policy follows strict retention timelines based on legal requirements. Once obligations are met, documents are permanently deleted.
- Retention periods follow licensing rules.
- Automatic deletion removes expired data.
- Secure wiping prevents recovery.
- Audits remove redundant information.
2026 Security Trends and KYC Protection
Security systems now include real-time monitoring and AI-based threat detection to protect stored data.
- Shorter certificate cycles improve encryption strength.
- AI monitoring detects suspicious activity.
- Regular audits validate system integrity.
- Continuous updates prevent vulnerabilities.
How Users Can Protect Their Own Data
Users also play a role in maintaining security. Following best practices helps prevent exposure.
- Verify the website before uploading documents.
- Remove unnecessary sensitive details.
- Avoid public Wi-Fi during uploads.
- Use secure communication channels.
Compliance and User Trust
The gembet privacy policy balances regulatory compliance with user trust. Verified accounts reduce fraud and improve platform reliability.
- Faster withdrawals after verification.
- Improved account security.
- Reduced fraud across the platform.
- Clear communication of requirements.
The gembet privacy policy remains a core component of platform security. Through encryption, restricted access, and strict handling procedures, user data remains protected.
As technology evolves, these systems continue to improve, ensuring that personal and financial information remains secure.
Gembet Data Protection Framework and Security Layers
Gembet Data Protection is built on a multi-layered security framework designed to protect user information from the moment it is submitted until it is permanently removed from the system. This framework combines encryption, controlled access, and continuous monitoring to reduce exposure to potential threats.
Instead of relying on a single security layer, the system distributes protection across multiple checkpoints. This ensures that even if one layer is tested, additional safeguards remain active to protect sensitive data.
This layered approach creates a more resilient environment where user information remains secure throughout its lifecycle.
How Gembet Data Protection Secures Document Uploads
The first stage of Gembet Data Protection begins during document submission. Files are encrypted before leaving the user’s device, ensuring that data cannot be intercepted in readable form.
Once uploaded, documents are immediately transferred into secure storage environments where additional encryption protocols are applied. This ensures that files remain protected even after the transfer process is complete.
- Encrypted transmission using modern protocols
- Secure storage with restricted access
- File validation to prevent tampering
- Isolation from general system databases
This process ensures that documents are protected at every stage of handling.
Access Control in Gembet Data Protection Systems
Access control is a key component of Gembet Data Protection. Not all personnel or systems have access to sensitive information, reducing the risk of internal exposure.
Permissions are assigned based on role and necessity. Only authorized systems or personnel can access specific types of data, and all interactions are logged for accountability.
This structured access model helps maintain strict control over how information is used.
Encryption Standards in Gembet Data Protection
Encryption plays a central role in Gembet Data Protection. Data is protected both during transmission and while stored on secure servers.
Modern encryption standards ensure that even if data is accessed without authorization, it remains unreadable. This significantly reduces the impact of potential breaches.
Regular updates to encryption protocols ensure that protection remains effective against evolving threats.
How Monitoring Enhances Gembet Data Protection
Continuous monitoring is essential for maintaining strong Gembet Data Protection. Systems analyze activity in real time to identify unusual patterns or potential threats.
Automated tools can detect irregular login attempts, abnormal data access, or unusual transaction behavior. When detected, these events trigger additional security checks.
This proactive approach helps prevent incidents before they escalate.
Data Minimization in Gembet Data Protection
One of the most effective strategies in Gembet Data Protection is limiting the amount of data collected. By only storing necessary information, the platform reduces overall risk exposure.
This approach simplifies data management and ensures that unnecessary information is not retained. It also reduces the potential impact of any security incident.
Data minimization supports both efficiency and security.
How Gembet Data Protection Handles Data Retention
Retention policies define how long data is stored and when it should be removed. Gembet Data Protection follows structured timelines based on regulatory requirements.
Once data is no longer required, secure deletion methods are used to remove it permanently. This ensures that information cannot be recovered after deletion.
- Defined retention periods based on compliance rules
- Automated deletion processes
- Secure wiping to prevent recovery
- Regular audits of stored data
This ensures that data does not remain in the system longer than necessary.
User Responsibility in Gembet Data Protection
While systems provide strong protection, users also play a role in maintaining security. Following best practices helps reduce the risk of unauthorized access.
Simple actions such as using strong passwords and verifying secure connections can significantly improve overall safety.
- Use unique passwords for each account
- Avoid sharing login credentials
- Verify secure connections before uploading files
- Log out after completing sessions
These steps complement the broader Gembet Data Protection framework.
Adapting Gembet Data Protection to Modern Threats
Security threats continue to evolve, requiring systems to adapt continuously. Gembet Data Protection integrates updated technologies to address new risks.
This includes improved encryption, advanced monitoring systems, and updated verification processes. By staying current, the platform maintains strong protection standards.
Adaptability ensures long-term effectiveness.
Transparency in Gembet Data Protection Practices
Transparency is an important part of Gembet Data Protection. Clear documentation helps users understand how their data is handled and protected.
Providing accessible information about data practices builds trust and allows users to make informed decisions.
This transparency strengthens the relationship between users and the platform.
Long-Term Benefits of Gembet Data Protection
Strong data protection systems provide long-term benefits for both users and platforms. They reduce the risk of data breaches, improve trust, and support regulatory compliance.
By maintaining consistent security practices, the platform creates a stable environment for ongoing use.
Users benefit from knowing that their information is handled with care and protected by modern systems.
Final Approach to Gembet Data Protection
Gembet Data Protection is not a single feature but a combination of systems working together to safeguard user information. From encryption and access control to monitoring and data management, each component contributes to overall security.
Understanding these elements helps users navigate the platform with greater confidence and awareness.
By maintaining a structured and adaptive approach, Gembet Data Protection continues to provide a reliable framework for protecting sensitive data in a changing digital environment.
Experience the real deal with SG's top Live Dealers. Play Baccarat, Roulette & more.