Gembet Privacy Policy: From SSL to TLS – ‘Invisible Shields’
Gembet privacy policy protocols serve as the primary defense mechanism between your personal information and the evolving threats of the digital landscape. While users focus on the odds and the variety of games, a sophisticated layer of encryption works silently to ensure that every interaction remains confidential. The shift from Secure Sockets Layer (SSL) to Transport Layer Security (TLS) represents a significant milestone in how modern platforms handle sensitive information.
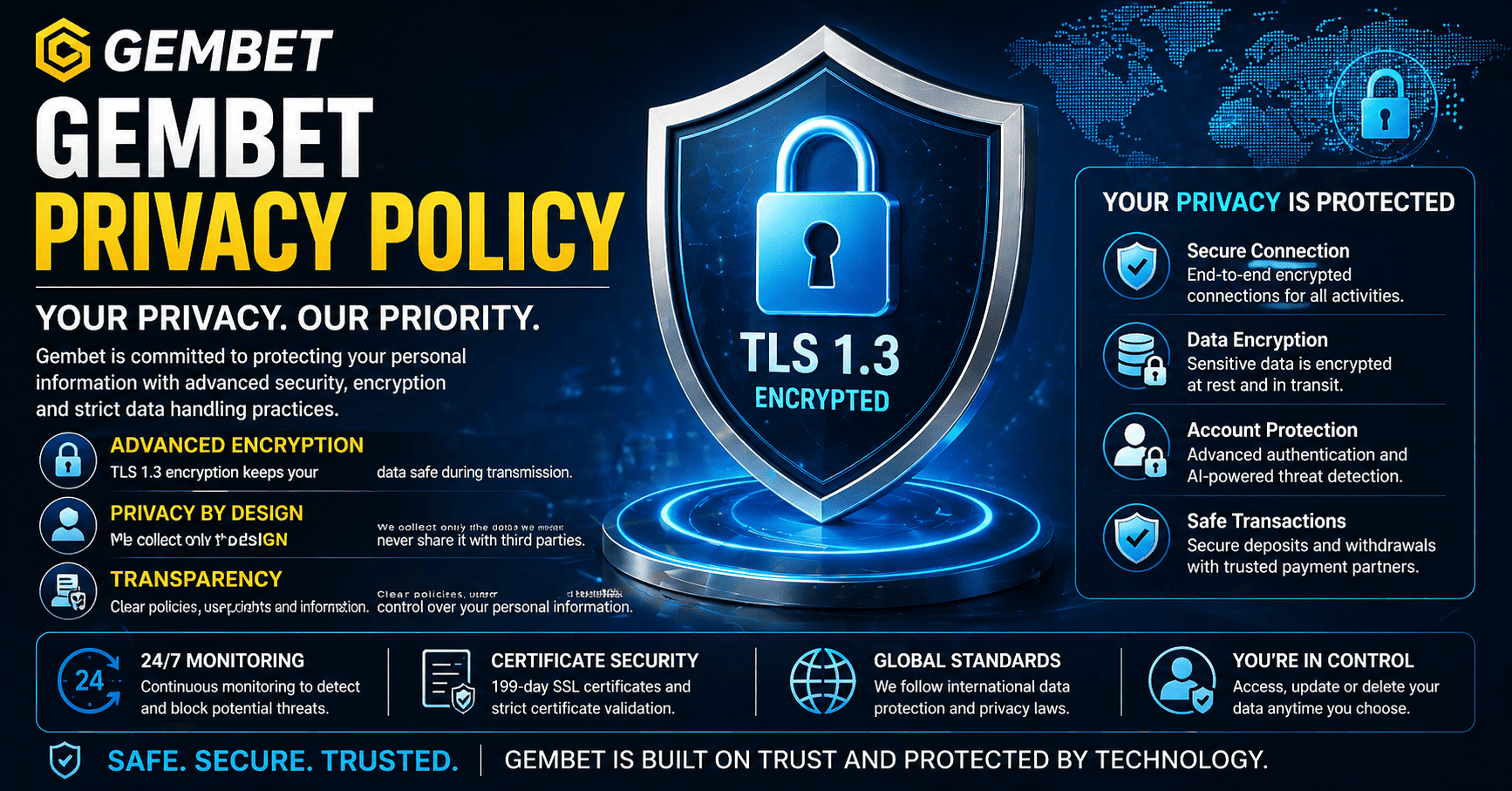
Maintaining high standards for data privacy in Gembet involves a multi-layered approach to security:
- Encryption of sensitive data during every stage of transmission.
- Verification of server identity to prevent phishing and spoofing.
- Continuous monitoring of traffic to identify and block potential exploits.
- Strict adherence to international regulations regarding the storage of personal details.
For anyone navigating an online platform in 2026, understanding the difference between these protocols is vital. Although the term SSL is still frequently used in common conversation, the industry has transitioned entirely to TLS to address fundamental security flaws. This evolution is central to the way the platform manages information, providing a robust framework that prevents unauthorized interception of data during transmission.
The Evolution of Security and the Gembet Privacy Policy
The gembet privacy policy was designed to adapt as cryptographic standards improve. SSL was the original standard for creating an encrypted link between a web server and a browser, but it eventually became susceptible to sophisticated hacking methods. Protocols like SSL 3.0 were found to have vulnerabilities that allowed attackers to perform man-in-the-middle attacks, effectively capturing data during a session.
To combat these risks, TLS was introduced as a more secure successor. By 2026, TLS 1.3 has become the global standard, offering several key advantages:
- Removal of legacy algorithms that were vulnerable to modern computing power.
- Faster connection times due to a more efficient handshake process.
- Enhanced forward secrecy, ensuring that even if a private key is compromised, past sessions remain encrypted.
- Mandatory encryption for the entire handshake, leaving no part of the initial connection visible to observers.
By prioritizing TLS 1.3, the platform ensures that user data protection is built into the connection itself. This technical foundation is a core component of the gembet privacy policy, providing a secure environment for all account-related activities.
How TLS 1.3 Enhances Data Privacy Gembet
The gembet privacy policy relies on the most advanced handshake process available today. In previous versions of security protocols, multiple messages had to travel back and forth between your device and the server before a secure connection was finalized. This created a window of opportunity for interference and slowed down the loading speed of the site.
The implementation of TLS 1.3 addresses these issues through:
- One Round-Trip Time (1-RTT) handshakes, which finalize the secure connection twice as fast as older versions.
- Zero Round-Trip Time (0-RTT) resumption, allowing returning users to send encrypted data on their very first message to the server.
- Strict Cipher Suite requirements, which force the use of only the strongest available encryption methods.
- Signed Certificate Timestamps (SCTs) to prove that certificates are logged in public, verifiable databases.
This efficiency improves the speed of the site while narrowing the window of opportunity for an attacker to disrupt the session. For the user, this means that user data protection is active from the very first millisecond of interaction. The gembet privacy policy documentation reflects these technical choices as part of a broader commitment to transparency.
2026 Certificate Standards for User Data Protection
In 2026, the landscape of web security changed with shorter validity periods for security certificates. The industry moved toward 199-day cycles, requiring the gembet privacy policy team to renew and re-verify their security credentials twice a year. While this requires more maintenance for the platform, it significantly increases security for the user.
Frequent certificate rotation provides several benefits for data privacy gembet:
- Reduced exposure time if a certificate is ever compromised.
- Regular identity verification, ensuring the platform remains in good standing with Certificate Authorities.
- Faster adoption of new security patches during the renewal process.
- Automated domain validation, which prevents fraudulent sites from maintaining long-term mimicry of the official platform.
The gembet privacy policy includes these rigorous auditing processes as a standard practice. Every 199 days, the platform must prove its legitimacy to independent security organizations. This cycle ensures that the protection of your information is never outdated.
AI Integration and Adaptive User Data Protection
As we move through 2026, artificial intelligence has become a standard component of cybersecurity within the gembet privacy policy framework. The platform uses AI-driven monitoring systems that analyze traffic patterns in real time to identify anomalies that might suggest a security threat.
These AI layers assist in user data protection by:
- Detecting credential stuffing attacks where hackers try lists of leaked passwords from other sites.
- Identifying bot behavior that mimics human interaction to scrape data or exploit account features.
- Flagging unusual login locations and triggering secondary authentication steps.
- Monitoring transaction velocity to prevent fraudulent withdrawals or deposits.
If the AI detects suspicious activity, it can automatically initiate a security challenge. This adaptive security layer works alongside encryption to provide a multi-layered defense. The gembet privacy policy continues to evolve as these systems improve.
Securing Financial Transactions and KYC Documents
Financial information is the most sensitive data handled by the platform, and the gembet privacy policy outlines specific measures to keep this information safe. The platform integrates with PCI-DSS compliant payment gateways, ensuring that full financial details are not stored on the main servers.
Key elements of data privacy gembet for financial security include:
- Tokenization of payment data, replacing card details with secure tokens.
- Encrypted document uploads for the Know Your Customer (KYC) process.
- Isolation of financial databases from gaming servers.
- End-to-end encryption for all withdrawal requests.
These user data protection mechanisms ensure that sensitive identity information remains secure throughout its lifecycle.
User Rights and Data Governance
The gembet privacy policy also defines how users can control their information. These rights align with international data protection standards.
Your rights include:
- The Right to Access: Request a copy of your stored data.
- The Right to Rectification: Correct inaccurate information.
- The Right to Erasure: Request deletion under certain conditions.
- The Right to Object: Opt out of specific data processing activities.
The platform follows data minimization principles, collecting only what is necessary to operate accounts and comply with regulations.
Protecting Your Connection on Different Devices
Whether using desktop or mobile, the gembet privacy policy maintains consistent protection standards. Mobile users, especially on public networks, require additional safeguards.
To maintain user data protection, the platform uses:
- HTTP Strict Transport Security (HSTS) to enforce encrypted connections.
- Certificate Pinning for secure mobile communication.
- Secure Cookie Handling to protect session tokens.
- Device Fingerprinting to verify login sources.
These measures ensure that data privacy gembet is maintained across all devices and connection types.
The transition to modern encryption standards reflects a continuous effort to protect users in an evolving digital environment. Through layered security, monitoring systems, and strict data policies, the gembet privacy policy provides a secure foundation for platform interaction.
Maintaining user data protection depends on updated protocols, regular audits, AI monitoring, and user control over personal information. These combined efforts ensure that data remains protected and the platform continues to meet modern security expectations.
As security standards evolve, the gembet privacy policy will continue adapting to ensure that personal and financial data remain protected under the latest innovations.
How Data Handling Practices Support User Trust
Trust in any online platform is built on how data is collected, stored, and used. While technical security measures protect information during transmission, data handling practices determine how that information is managed over time.
The Gembet Privacy Policy outlines how user data is processed in a way that prioritizes both functionality and protection. This includes limiting access to sensitive information and ensuring that only necessary data is retained.
By maintaining clear boundaries around data usage, platforms create a more transparent environment where users understand how their information is handled.
The Role of Encryption Beyond Transmission
Encryption is often associated with data transfer, but its role extends beyond that. Stored data must also remain protected to prevent unauthorized access.
Modern systems apply encryption at rest, meaning that even if data storage is compromised, the information remains unreadable without the proper decryption keys.
This additional layer complements the Gembet Privacy Policy by ensuring that data remains secure not only during transmission but throughout its entire lifecycle.
Managing Access Control and Permissions
Access control is a key component of data security. Not all system components or personnel require access to the same information.
By implementing strict permission levels, platforms can limit exposure and reduce the risk of internal vulnerabilities. Each access point is monitored and logged to ensure accountability.
These controls work alongside the Gembet Privacy Policy to create a structured system where sensitive data is only available to authorized processes.
How Regular Audits Improve Security Standards
Security is not a one-time implementation but an ongoing process. Regular audits help identify weaknesses and ensure that systems remain up to date with current standards.
These audits may include vulnerability testing, compliance checks, and system reviews. By continuously evaluating performance, platforms can address potential risks before they become issues.
This ongoing review process strengthens the effectiveness of the Gembet Privacy Policy and ensures that it adapts to evolving threats.
Minimizing Data Collection for Better Privacy
One of the most effective ways to protect user information is to limit how much data is collected in the first place. Data minimization reduces exposure and simplifies security management.
Only essential information should be stored, and unnecessary data should be avoided or removed. This approach lowers the risk of data breaches and improves overall efficiency.
By focusing on essential data only, the Gembet Privacy Policy supports a cleaner and more secure system.
How Users Can Enhance Their Own Data Security
While platforms implement advanced security measures, users also play a role in protecting their own information. Simple habits can significantly reduce the risk of unauthorized access.
- Use strong and unique passwords for accounts
- Avoid sharing login details across multiple platforms
- Enable additional verification steps when available
- Log out after completing sessions on shared devices
These actions work together with the Gembet Privacy Policy to create a more secure environment for both the platform and its users.
Adapting to Future Security Developments
Technology continues to evolve, and security practices must adapt accordingly. New encryption methods, authentication systems, and monitoring tools are constantly being developed.
Platforms that stay updated with these advancements are better prepared to handle emerging threats. This adaptability ensures that data protection remains effective over time.
The Gembet Privacy Policy reflects this ongoing evolution by incorporating new technologies and refining existing processes.
Maintaining Transparency in Data Policies
Transparency is an important aspect of user trust. Clear documentation helps users understand how their data is handled and what protections are in place.
Providing accessible explanations of data usage allows users to make informed decisions about their interactions with the platform.
Through clear communication, the Gembet Privacy Policy ensures that users remain informed about how their information is managed.
Long-Term Data Protection Strategy
Effective data protection requires a long-term strategy that combines technology, processes, and user awareness. Each component contributes to the overall security of the platform.
This includes maintaining updated encryption standards, performing regular system checks, and educating users about best practices.
By combining these elements, the Gembet Privacy Policy supports a stable and secure environment for ongoing platform use.
Final Approach to Data Privacy and Security
Data privacy is not a single feature but a combination of multiple systems working together. From encryption and access control to audits and user awareness, each element plays a role in maintaining security.
Understanding these components helps users navigate platforms with greater confidence and awareness.
By maintaining a structured and adaptive approach, the Gembet Privacy Policy continues to provide a reliable framework for protecting user information in an evolving digital landscape.
Experience the real deal with SG's top Live Dealers. Play Baccarat, Roulette & more.